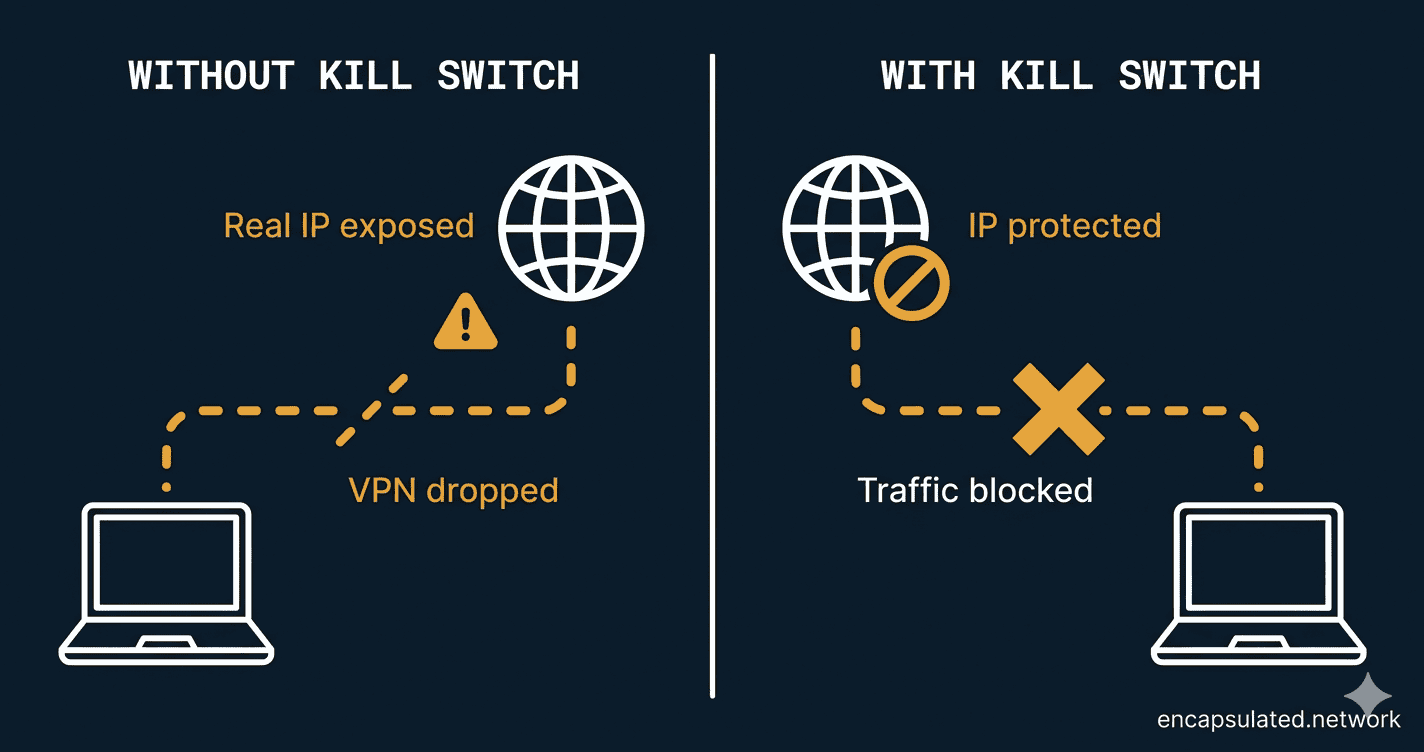
Your VPN drops for two seconds. You don’t notice — you’re mid-scroll, nothing freezes, no error message appears. But in that two-second window, your device reconnected to the internet without VPN protection. Your real IP address was visible to every server you contacted. Your ISP could see your traffic. If you were torrenting, your real IP just appeared in the peer swarm.
A VPN kill switch exists entirely to prevent that scenario. It’s the one feature that makes the difference between a VPN that protects you consistently and one that only protects you most of the time.
This article explains what a kill switch actually is, how it works under the hood, why some kill switches fail even when they’re turned on, and how to test whether yours is doing its job.
What Is a VPN Kill Switch?
A VPN kill switch is a security failsafe that automatically cuts your device’s internet connection the moment your VPN connection drops. No human input required — it detects the dropout and blocks all outgoing traffic before any unencrypted data can reach the public internet.
Think of it like a circuit breaker in your home’s electrical panel. Under normal conditions it does nothing — power flows freely. The moment there’s a fault, it trips instantly and cuts the circuit before any damage can spread. A kill switch works the same way: invisible when everything is fine, automatic and immediate when something goes wrong.
The problem a kill switch solves is timing. When your VPN is running normally, all your traffic flows through an encrypted tunnel. Your real IP address is hidden behind the VPN server’s IP. But VPN connections aren’t perfectly stable — they can and do drop, even briefly. In that gap, your device falls back to your regular unprotected internet connection. A kill switch closes that gap by blocking the fallback entirely.
Why Do VPN Connections Drop?
Before understanding how a kill switch responds, it helps to know what it’s responding to. VPN connections drop more often than most people realise, and the causes vary.
Network switching is the most common culprit. Moving from Wi-Fi to mobile data, walking out of range of one router and connecting to another, or resuming from sleep — each of these forces your device to re-establish its network connection, which temporarily interrupts the VPN tunnel.
Server-side issues also play a role. If the VPN server you’re connected to becomes overloaded, times out, or goes offline for maintenance, your client loses the tunnel. Most VPN apps reconnect automatically, but there’s always a window between the drop and the reconnect.
Protocol instability can matter too. UDP-based VPN connections are faster but less reliable than TCP — they don’t guarantee packet delivery, so a burst of packet loss on a congested network can cause the tunnel to collapse. This is why some VPN apps offer a TCP fallback option for unreliable connections.
Software interference occasionally causes drops. Overzealous firewall or antivirus software may flag the VPN tunnel and interrupt it, particularly after a software update changes detection signatures.
None of these causes are rare edge cases. On a mobile device in a city, your VPN might drop and reconnect dozens of times a day as you move between networks. Without a kill switch, each of those reconnects is a brief exposure window.
How Does a VPN Kill Switch Work?
Most kill switches operate in a continuous four-step loop running in the background: Observe (monitor the VPN connection status), Detect (identify a dropout), Block (immediately sever internet access), and Restore (re-enable access once the tunnel is back). This loop runs constantly while the VPN is active — the cycle time is typically milliseconds.
The implementation under the hood varies by platform, but the most reliable approach uses the operating system’s own firewall to do the blocking:
- Linux —
iptablesornftablesrules that drop all traffic not routed through the VPN interface. For copy-paste UFW and nftables kill switch implementations on Linux — including both the accessible UFW method and the more advanced kernel-enforced nftables ruleset — see the security hardening section of our Linux VPN setup guide. - Router-level (OpenWRT / DD-WRT) — firewall rules that set the WAN forward policy to Reject, blocking all traffic when the VPN interface is down. On Asus Merlin and GL.iNet, a kill switch toggle handles this automatically. For the full per-firmware implementation, see the security hardening section of our VPN router setup guide.
- macOS — Packet Filter (PF) rules applied at the kernel level
- Windows — Windows Filtering Platform (WFP), the same subsystem used by the Windows firewall
Using OS-level firewall rules is significant because it means the traffic block happens at the kernel level — not inside the VPN application itself. If the VPN app crashes entirely, the firewall rules are still in place.
A second implementation method is interface binding. Instead of actively blocking traffic, some implementations force applications to bind exclusively to the VPN network interface (typically tun0 for OpenVPN or wg0 for WireGuard). If that interface disappears when the VPN drops, the bound app simply has no route to the internet. There’s no door to open.
Some providers and reviewers distinguish between two implementation styles, sometimes called active and passive — though these aren’t standard industry terms you’ll find consistently across provider documentation. In the active model, the kill switch signals the OS to stop all traffic the moment a dropout is detected. In the passive model, it simply waits for the VPN server’s signal to disappear before closing the gate. The practical difference is response speed: active detection is faster, while passive introduces a small lag between dropout and block.
System-Level vs. App-Level Kill Switches
Not all kill switches work the same way, and the difference matters in practice.
| System-Level | App-Level | |
|---|---|---|
| What it blocks | All internet traffic on the device | Only the selected applications |
| How it works | OS firewall rules (iptables, PF, WFP) | VPN app monitors and kills specific processes |
| If the VPN app crashes | Firewall rules remain — still protected | Protection may fail along with the app |
| Disruption level | High — all connectivity stops | Low — other apps keep running |
| Best for | High-privacy use cases, torrenting, journalism | Casual users who only need to protect specific apps |
A system-level kill switch is the more secure option. An app-level kill switch is more convenient — for example, you can configure only your torrent client to shut down on a dropout while your browser keeps working normally.
Android: The Built-In Kill Switch You Should Know About
Android 8.0 and later includes a native system-level kill switch that works independently of any VPN app. It’s one of the most underused privacy features on any platform.
To enable it: Settings → Network & Internet → VPN → tap the gear icon next to your VPN → enable “Block connections without VPN.“ (This is the stock Android path. Samsung devices typically use Settings → Connections → More connection settings → VPN; Xiaomi and other manufacturers may vary — search “VPN settings” in your device’s Settings search bar if the path differs.)
This uses Android’s own OS-level controls to block traffic whenever the VPN isn’t active. Because it operates at the system level and outside the VPN app, it will hold even if the VPN app crashes or is force-closed. If you’re on Android, this is worth enabling alongside your VPN app’s own kill switch setting — they complement each other. For a full walkthrough of setting up a VPN on Android — including always-on VPN, Lockdown Mode, Private DNS, and the battery optimization step — see our Android VPN setup guide.
iOS: A More Accurate Picture
The iOS kill switch story is better than its reputation suggests — but it still comes with caveats worth understanding.
iOS 14 (released 2020) introduced the includeAllNetworks property in Apple’s NetworkExtension framework, which forces all network traffic through the VPN tunnel at the OS level. When the tunnel drops, the system drops all traffic rather than allowing it to fall back to an unprotected connection. This is functionally equivalent to a system-level kill switch, and several major providers now implement it: IVPN, ExpressVPN, NordVPN, and Surfshark all offer kill switch functionality on iOS as of 2024–2025.
The limitation that previously made iOS kill switches unreliable — App Store restrictions preventing network-level traffic interception — was always a mischaracterisation. The actual constraint was the NetworkExtension framework’s API capabilities, which Apple expanded with includeAllNetworks. The restriction no longer applies in the same way.
That said, iOS is not identical to desktop. Even with includeAllNetworks enabled, some system traffic is exempt from the VPN tunnel: DHCP, captive portal detection, VoLTE calls, and certain companion device communication. For the vast majority of users this is an acceptable trade-off. For those in high-risk environments where any exemption is unacceptable, desktop or Android with a system-level kill switch remains the more controlled option.
The practical takeaway: if your VPN app offers a kill switch toggle on iOS, enable it. Check your provider’s iOS release notes to confirm they have implemented includeAllNetworks — not all providers have updated their iOS apps to use it.
Fire OS (Amazon Fire TV Stick)
Fire OS does not expose Android’s system-level “Block connections without VPN” toggle, and there is no equivalent lockdown mechanism available through the settings menu on any current Firestick model. Kill switch protection on Fire TV is entirely app-level — your VPN app must include its own kill switch feature and it must be enabled within the app’s settings. If the VPN app crashes or is terminated by the system under memory pressure, the kill switch goes down with the app, because the kill switch is a feature of the app rather than the platform. This is a meaningful architectural limitation compared to Android’s Lockdown Mode or the router-level kill switch implementations covered in the router VPN setup guide. For the full breakdown of how kill switches work on Firestick — and when the router workaround is the more reliable option — see the Firestick VPN setup guide.
The Reboot Vulnerability: When Kill Switches Fail
Here’s something most VPN providers don’t advertise: many kill switches fail during a system reboot.
The reason is a timing problem. When your computer restarts, the operating system establishes an internet connection early in the boot sequence — before the VPN app has loaded and before its firewall rules are in place. In that window, your device is online without VPN protection. If any app or system service communicates during boot, that traffic goes out unencrypted.
For most casual VPN users, this is an acceptable trade-off. For journalists, activists, or anyone in a high-risk environment, it is not.
The fix is to look for a VPN that offers what some providers call a Permanent Kill Switch or Advanced Kill Switch mode. This works by writing persistent firewall rules that survive a reboot — the rules are active from the moment the OS loads, before the VPN app itself starts. ProtonVPN offers this on Windows and Linux (not macOS). Mullvad offers it on Windows and Linux as well, and calls it Lockdown Mode.
macOS is a harder case. Apple does not allow system services to specify start-up dependencies or load order, which means even the best providers cannot reliably enforce firewall rules before the OS establishes its initial network connection. Mullvad’s own documentation acknowledges a known boot-time leak window on macOS that cannot currently be fully closed. If you’re on macOS and boot-time protection is a firm requirement, be aware of this limitation regardless of which provider you use.
Should You Turn Your Kill Switch On?
For most users, the answer is yes — leave it on. The downside is occasional brief connectivity interruptions when your VPN reconnects, which is a minor inconvenience. The upside is consistent protection. That said, whether you need it varies by what you’re doing.
When It’s Non-Negotiable
- Public Wi-Fi — Coffee shops, airports, hotels. Untrusted networks are where a momentary IP exposure is most likely to be seen by someone who shouldn’t see it. A kill switch is essential here.
- Torrenting and P2P — When you’re connected to a BitTorrent swarm, every peer in that swarm can see the IP address you’re connecting from. If your VPN drops for two seconds without a kill switch, your real IP gets logged by every peer in the swarm for that window. Enable the kill switch and leave it on.
- Journalists, activists, and researchers — If a single IP exposure has professional, legal, or personal safety implications, a kill switch is a baseline requirement, not an optional feature. Pair it with a permanent kill switch if boot-time protection matters, and verify your provider operates a verified no-log policy — a kill switch protects your IP during dropouts, but only a no-log architecture protects you from the provider itself.
- Countries with restricted VPN usage — Where VPN use itself may attract scrutiny, an unprotected window during a dropout can expose that you’re using one at all.
When You Might Toggle It Off
- Streaming on a stable home connection — A kill switch during a brief VPN reconnect will pause your stream rather than just buffering through it. If you’re using a VPN only for geo-unblocking on a reliable home network, the reconnect disruption may be more annoying than the privacy risk is concerning. Toggle off if it bothers you.
- Windows with a Microsoft account login — If your Windows account requires internet access to authenticate on login (common with Microsoft 365 accounts), an active kill switch can prevent you from signing in after a reboot. Temporarily disable it during login, then re-enable.
The underlying principle: the kill switch protects the 0.1% of the time your VPN drops. For most users that’s a sensible default to leave on. For high-risk use cases, it’s non-negotiable. For low-stakes streaming, the interruptions may outweigh the benefit — your call.
How to Test If Your Kill Switch Actually Works
Turning a kill switch on in settings doesn’t guarantee it works. Testing it takes two minutes and is worth doing once on any VPN app you rely on.
Test 1: The Force-Kill Test
This is the most direct test. Connect to your VPN, then while connected, force-close the VPN application entirely:
- Windows: Open Task Manager → find the VPN process → End Task
- macOS: Open Activity Monitor → find the VPN process → Force Quit
Immediately try to load a website. If the page loads, your kill switch failed — your internet kept working after the VPN app was killed. If the page won’t load and you see a connection error, the kill switch is working. Reopen your VPN app to restore the connection.
Test 2: The Wi-Fi Toggle Test
Before running this test, open icanhazip.com in a browser tab — it returns only your current IP address, nothing else, on a plain page. Then, while connected to your VPN, disconnect and immediately reconnect your Wi-Fi.
Watch the page carefully as your connection restores. If your real IP address appears at any point before the VPN reconnects, the kill switch either isn’t active or is too slow to catch the dropout. You should see a connection failure or error until the VPN tunnel is back — not your real IP.
Test 3: Wireshark (Advanced)
For a more thorough check, use Wireshark to monitor your network interface during a simulated crash. Filter for traffic not originating from your VPN interface. If packets appear on your regular network interface during a VPN dropout, your kill switch has a gap. This level of testing is for users who need high confidence — security researchers, journalists, or anyone in a sensitive environment.
Kill Switch and Split Tunneling
These two features are often discussed together because they sit at opposite ends of the same spectrum: split tunneling routes some traffic outside the VPN by design; a kill switch blocks all traffic outside the VPN when it drops. In most configurations, they conflict.
On the majority of platforms, enabling split tunneling with a system-level kill switch active will produce unpredictable results — some implementations disable split tunneling when the kill switch is on, others allow it but leave the excluded apps unprotected during a dropout.
Some VPN providers on Windows (Mullvad is the clearest example) offer a more nuanced configuration: apps routed through the VPN are blocked by the kill switch on dropout, while apps explicitly excluded from the tunnel continue working normally. This is the most sensible implementation of the two features together, but it’s not universal.
If you use both features, check your specific VPN app’s documentation for how they interact. Don’t assume they work cleanly together without verifying it. For a full explanation of how split tunneling works and when to use it, see our split tunneling guide.
Frequently Asked Questions
Does a VPN kill switch slow down my internet?
No. A kill switch monitors your VPN connection status in the background but doesn’t process or filter your actual traffic while the VPN is running normally. It has no measurable impact on speed. The only time it affects your connection is when it activates — at which point it’s intentionally stopping traffic, not slowing it.
Should I always leave my kill switch on?
For most users, yes. The downside is occasional brief connectivity interruptions during VPN reconnects — typically a few seconds. The upside is that your real IP address never leaks during those drops. The main exception is if you’re using a VPN exclusively for streaming on a stable home connection, where reconnect interruptions may be more disruptive than the privacy risk warrants.
Can I use a kill switch and split tunneling at the same time?
It depends on your VPN app and platform. On most implementations, a system-level kill switch will conflict with split tunneling. Some providers on Windows — Mullvad being the clearest example — allow the kill switch to protect VPN-routed apps while excluded apps continue running. Check your VPN app’s documentation before assuming they work together.
My internet stopped working even though the VPN is off. What’s happening?
Your kill switch is still active. This happens when the VPN app is closed without properly disabling the kill switch first, leaving the firewall rules in place. The fix is to reopen the VPN app and either reconnect or explicitly turn the kill switch off in settings. If the VPN app won’t open, you may need to temporarily disable your OS firewall or flush firewall rules manually — check your VPN provider’s support documentation for the specific steps.
What’s the difference between a kill switch and a DNS leak?
They protect against different failure modes. A DNS leak happens while your VPN is running — your device sends DNS queries outside the VPN tunnel, potentially revealing the websites you’re visiting to your ISP even though your main traffic is encrypted. A kill switch protects against what happens when your VPN drops entirely. A VPN can have a working kill switch and still have a DNS leak problem — they’re separate issues. See our DNS leak test guide for how to check for and fix that separately.
The Bottom Line
A VPN kill switch is the feature that turns “mostly private” into “consistently private.” Most VPN connections are stable most of the time — but most of the time isn’t good enough if you’re on public Wi-Fi, torrenting, or operating in a high-risk environment where a two-second exposure window has consequences.
Turn it on. Test it using the force-kill method above so you know it works — don’t assume the setting being toggled means the behaviour is correct. If you’re on Android, enable the OS-level “Block connections without VPN” setting as a secondary layer regardless of what your VPN app offers. And if boot-time protection matters to you, look specifically for a provider that offers a permanent or advanced kill switch mode.
Understanding how your VPN handles battery and always-on behaviour on mobile is a related consideration worth reading alongside this — a kill switch that fires frequently on a spotty mobile connection will also affect how much battery the VPN draws during reconnects.