You opened your VPN app, tapped into the settings, and found it there: split tunneling. Somewhere under Advanced, or Connection, or maybe just sitting in its own toggle. No explanation. Just a name that sounds like something might get cut in half.
Most people either ignore it or turn it on and hope for the best. Neither is the right move.
Split tunneling is one of the most genuinely useful settings in any VPN app — once you understand what it actually does. This guide explains the concept from scratch, walks through five real situations where it solves a real problem, and tells you honestly when you should leave it switched off entirely.
What Is VPN Split Tunneling?
To understand split tunneling, you need to understand what your VPN does by default.
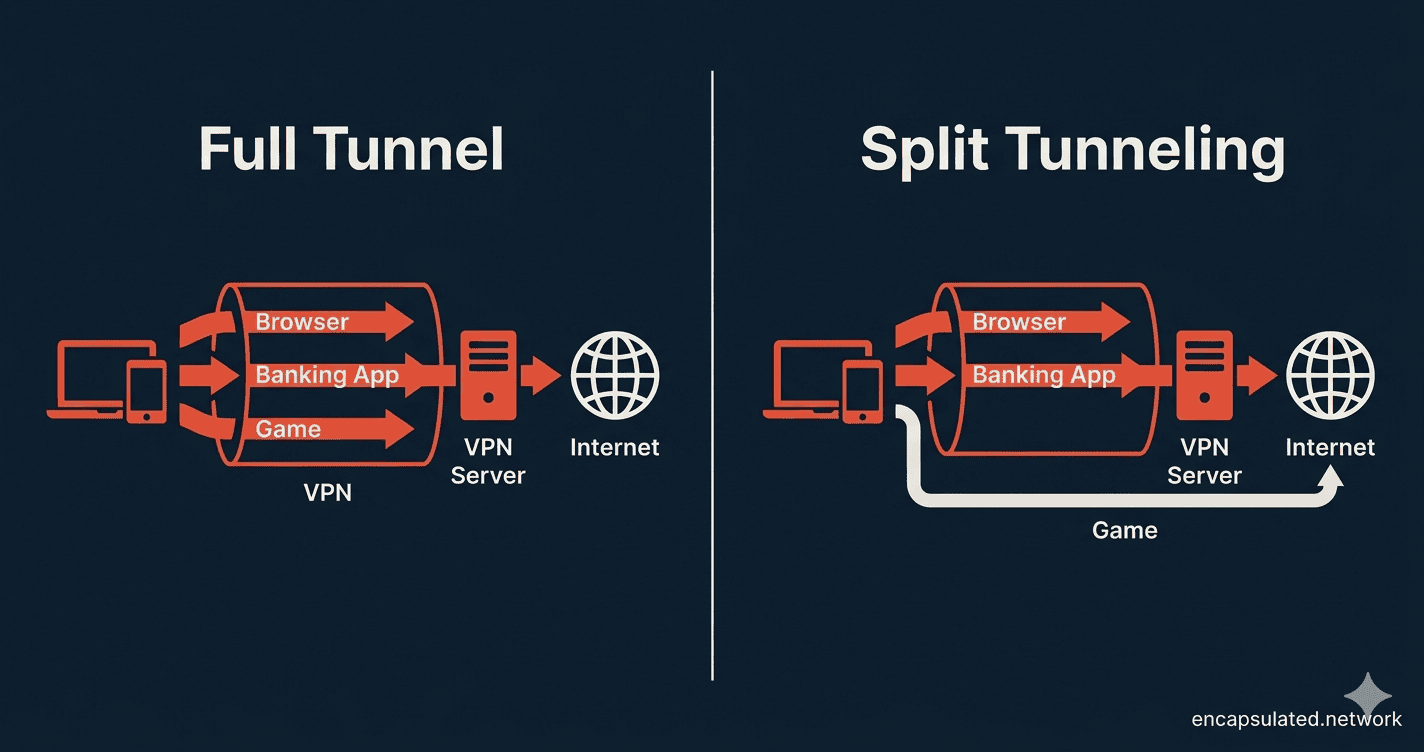
When split tunneling is off, your VPN runs in full tunnel mode: every single piece of data leaving your device — your browser, your apps, your background updates, everything — is encrypted and routed through the VPN server before reaching the internet. It is a single covered pipe. Nothing escapes it.
Split tunneling changes that. It lets you divide your traffic into two paths: one that goes through the encrypted VPN tunnel, and one that connects directly to the internet as normal. You decide which apps or websites take which route.
Think of your internet connection as a motorway. Full tunnel mode sends every vehicle — every car, lorry, and motorbike — through one private, covered bridge. Split tunneling lets you open a second lane: some vehicles take the private bridge, others take the open road. You control the traffic rules.
The setting is usually found under Advanced or Connection in your VPN app. Some providers label it differently — “per-app VPN,” “app exclusions,” or “bypass.” It is the same feature under different names.
The Three Types of Split Tunneling
Not all split tunneling works the same way. Most VPN providers offer at least one of the following three approaches, and understanding the difference helps you configure it correctly.
App-Based Split Tunneling
This is the most common type. You select specific applications — your browser, a game, a streaming app — and assign them to either the VPN tunnel or the direct connection. Everything else follows the default (usually the full tunnel). It is the most straightforward option and covers the majority of use cases.
URL and Domain-Based Split Tunneling
Instead of choosing by app, you specify particular websites or domains. Traffic to yourbank.com, for example, always bypasses the VPN and connects with your real IP address. Everything else stays encrypted. This requires more precise configuration but gives you finer control — useful when you need one specific service to see your real location, not the entire app it lives in.
Inverse Split Tunneling
This flips the default. Rather than picking what to exclude from the tunnel, you pick the one or two apps that should use the VPN. Everything else connects directly. It is the right approach when you only need VPN protection for a single purpose — a work tool, a privacy-sensitive app — and want everything else to run at full speed without overhead.
Five Situations Where Split Tunneling Actually Helps
Split tunneling is not a feature you use for the sake of it. These are the five real-world situations where it solves a concrete problem.
1. Your Printer or Smart TV Disappeared
This is the most common frustration for anyone who runs a VPN at home. You turn on the VPN, open the print dialog, and your printer is gone. Or your smart TV stops showing up in your casting menu. Or your NAS drive becomes unreachable.
The reason is straightforward: full tunnel mode routes all your traffic through a remote VPN server. From your device’s perspective, it is no longer on your local network — it is connected to a server somewhere else. Local devices on your home network, which communicate using LAN addresses, become invisible.
Split tunneling fixes this immediately. Exclude your local network traffic or the specific app you use to print, and your device stays visible to everything on your home network while your browser and other apps remain protected.
2. Your Banking App Is Blocking You
Banks flag VPN IP addresses as a fraud signal. A login from a VPN exit node in a different city — or a different country — looks suspicious to automated fraud systems, and your session may be blocked, flagged, or forced through additional verification every time.
With app-based split tunneling, you route your banking app directly through your real IP address while every other app on your device stays inside the VPN tunnel. You get normal, uninterrupted access to your bank, and everything else remains private. The same applies to any service that rejects VPN addresses — government portals, insurance sites, some payment processors.
3. Speed-Sensitive Tasks — Gaming, Downloads, Video Calls
VPN encryption adds processing overhead to every packet your device sends and receives. On a fast connection, the impact is modest. But for latency-sensitive tasks — online gaming, large file downloads, video calls where a few hundred milliseconds of lag is noticeable — that overhead has a real cost. The size of that overhead depends largely on which VPN protocol you are using — WireGuard carries significantly less overhead than OpenVPN for most use cases.
Routing those specific apps outside the tunnel removes the encryption overhead for those tasks only, without exposing everything else you are doing. Your game client connects directly; your browser stays protected. It is worth noting that this does not make your VPN faster — it simply stops applying VPN overhead to apps that do not need privacy protection. For a full breakdown of how encryption affects performance and battery life on mobile, see our guide on VPN battery drain on mobile.
4. Remote Work on a Corporate VPN
Many corporate VPN setups route all employee traffic through company servers by default — meaning your personal browsing, your streaming, your home devices all travel through your employer’s infrastructure. This is slow, creates unnecessary load on corporate networks, and in some configurations means your employer’s IT team can see everything.
Inverse split tunneling solves this cleanly. Only the work tools that need the corporate VPN — your internal database, your company file server, your business email — go through the tunnel. Everything personal connects directly as normal. This is the configuration most IT departments actually recommend when they trust users to set it up correctly.
5. Local Content and Location-Sensitive Apps
Some services are built around your real location. Food delivery apps, local streaming services, transit apps, and anything that uses your actual city for results will behave incorrectly — or refuse to work — when they see a VPN exit IP. Splitting these apps to connect directly, while your browser remains tunnelled, lets both work simultaneously without conflict.
The Risks — What Split Tunneling Does Not Protect
Split tunneling is a deliberate trade-off. The value is worth understanding clearly, and so is the exposure.
Unprotected traffic is fully exposed. Your VPN traffic travels through an encrypted, opaque pipe — no one in the middle can read it. Traffic running outside the tunnel is a different matter entirely. It travels on the open internet with no VPN encryption at all. Your ISP can see it. Anyone monitoring the network you are connected to can see it. Your real IP address is visible. There is no tunnel around it — it is simply regular, unencrypted internet traffic.
Real IP and location exposure. Every app you route outside the tunnel reveals your actual IP address and, by extension, your approximate location. For apps where that is intentional — your banking app, your printer — this is fine. For apps you simply forgot to configure, it is an accidental exposure.
Compromised apps on unprotected connections. If an app running outside the tunnel is compromised — by malware, a rogue update, or a hijacked connection — that malware can communicate freely with an attacker’s server, entirely undetected by any VPN-level monitoring. The more concrete risk for most users is simply that the compromised app’s traffic is unprotected and visible. In corporate environments with network-level split tunneling, security teams also worry about lateral movement from the unprotected side into secured internal systems — which is one reason IT departments apply stricter controls on managed devices.
Forgetting what is protected. The quietest risk of all. After configuring split tunneling, it is easy to lose track of which apps are inside the tunnel and which are not. Sensitive tasks performed in an unprotected app — because you forgot it was excluded — are exposed without any warning.
Split Tunneling vs Full Tunnel — When to Use Each
| Split Tunneling | Full Tunnel | |
|---|---|---|
| Privacy protection | Selective — chosen apps only | Complete — all traffic |
| Speed impact | Lower on direct apps | Uniform overhead on all apps |
| Battery drain | Reduced | Higher |
| Local network access | ✅ Works normally | ❌ Often breaks |
| Best for | Home use, remote work, mixed tasks | Public Wi-Fi, sensitive data, high-risk situations |
Enable split tunneling if: you need access to local network devices, your banking or payment app is being blocked, you are gaming or on a video call, or you are on a corporate VPN and want to separate work and personal traffic.
Keep full tunnel on if: you are connected to public Wi-Fi in a café, airport, or hotel; you are handling genuinely sensitive data; or your threat model requires that no traffic leaves your device unencrypted under any circumstances.
Platform Support — Does Your Device Actually Have It?
Split tunneling support varies significantly depending on your operating system. Before spending time configuring it, check whether your device supports it at all.
Windows and Android offer the broadest support. The majority of VPN providers with split tunneling implement it fully on both platforms, and app-based exclusions generally work as expected. If you are setting up a VPN on Android from scratch, the full process — including how to configure split tunneling alongside always-on VPN and kill switch settings — is covered in our Android VPN setup guide. If you want split tunneling at the network level — routing specific devices through the VPN while others connect directly, without configuring anything on individual phones or laptops — that is handled through policy-based routing on a router VPN. Asus Merlin’s VPN Director and OpenWRT’s LuCI PBR app are the most capable implementations of this approach.
macOS has historically been inconsistent. Apple’s sandboxing rules limit how third-party apps can intercept and reroute system-level network traffic, and several major providers dropped macOS split tunneling support in earlier OS versions. The current picture is more positive: multiple providers including Surfshark, PIA, and Mullvad added or restored macOS split tunneling support between 2024 and 2025, and ExpressVPN re-introduced it in late 2025. NordVPN remains a notable exception with no macOS support at the time of writing. The practical advice remains the same: check your specific provider’s documentation for your macOS version before relying on it.
iOS is the most restricted platform. Apple’s security architecture prevents most VPN apps from selectively routing traffic, and the majority of major providers — including NordVPN, ProtonVPN, and ExpressVPN — do not offer split tunneling on iPhone. That said, a small number of providers have found workarounds: Surfshark offers website-level exclusions on iOS, and IPVanish offers app-level split tunneling, making it one of the few consumer providers to do so. If you need reliable split tunneling across all apps, Android remains the significantly more capable platform — but it is worth checking your specific provider’s iOS documentation before assuming it is unavailable entirely.
On Fire OS devices, split tunneling is handled within your VPN provider’s app — the same app-level approach as Android, with no system-level control surface. On Vega OS devices — the Fire TV Stick 4K Select (2025) and Fire TV Stick HD (2026) — the situation is more constrained: Vega OS does not run Android APKs, sideloading is unavailable, and split tunneling is entirely dependent on whether your provider’s Vega-native app includes the feature. If network-level split tunneling matters — routing your Firestick through the VPN while other household devices connect directly, or vice versa — that is handled through policy-based routing at the router level rather than on the device itself. The Firestick VPN setup guide covers both paths.
Troubleshooting — When Split Tunneling Breaks
Split tunneling is not always plug-and-play. These are the three problems that come up most often, and how to resolve them.
The DNS Leak Problem
DNS leaks are the most common split tunneling failure — and they can go in two directions. The more significant concern is that apps you have configured to use the VPN tunnel still send their DNS queries — the requests that translate domain names like bbc.co.uk into IP addresses — to your ISP’s DNS resolver instead of the VPN’s. This means the domains you visit are visible to your ISP even though your traffic is supposedly tunnelled. A secondary issue can also occur in the opposite direction: excluded apps that should connect directly may still try to use the VPN’s DNS resolver, causing those apps to fail to load sites at all.
Both problems are especially common on Windows, where the operating system’s DNS behaviour does not always follow VPN routing rules cleanly.
The Windows Fix
On Windows 10 and Windows 11, the culprit is usually a feature called Smart Multi-Homed Name Resolution. When enabled, Windows sends DNS queries to all available DNS resolvers simultaneously and uses whichever responds first — which means queries can leak to your ISP’s DNS server even when your VPN’s resolver should be handling them.
To disable it: open the Group Policy Editor (gpedit.msc), navigate to Computer Configuration → Administrative Templates → Network → DNS Client, and set Turn off smart multi-homed name resolution to Enabled. This forces Windows to respect the DNS resolver assigned by your active network connection rather than querying all of them in parallel.
Note: Group Policy Editor is only available on Windows Pro and Enterprise editions. Windows Home users may need to apply the equivalent registry change directly.
How to Verify Your Setup Is Working
Once you have configured split tunneling, verify it is doing what you intended before relying on it. The simplest method:
- Visit ipleak.net in a browser that is routed through the VPN — confirm it shows your VPN’s IP address, not your real one.
- Open an app that you have configured to bypass the VPN and check its reported IP address — confirm it shows your real IP.
- If a bypassed app is showing the VPN IP, your routing rules are not applying correctly. If a tunnelled app is showing your real IP, you have a DNS or routing leak.
Running both checks takes two minutes and confirms your configuration is working as intended on both sides of the split.
Frequently Asked Questions
Does split tunneling make my VPN faster?
Not exactly. Split tunneling does not speed up your VPN connection — it removes VPN overhead from apps that you have routed outside the tunnel. Those apps connect at your normal internet speed because they are no longer encrypted by the VPN. Your tunnelled apps run exactly as they did before. The overall result can feel faster if you were previously routing high-bandwidth apps like streaming or gaming through the VPN unnecessarily.
Is split tunneling safe for banking?
Yes — and for banking specifically, it is often the better choice. Banks flag VPN IP addresses as fraud signals, so connecting with your real IP via split tunneling avoids blocked sessions or repeated verification prompts. Your banking traffic is still encrypted by your bank’s own HTTPS connection, which is the same protection you would have without any VPN at all. The risk is not exposing your banking traffic — it is accidentally routing other sensitive apps outside the tunnel when you did not intend to.
Is split tunneling the same as a kill switch?
No — they solve completely different problems. A kill switch cuts all internet access if the VPN connection drops unexpectedly, preventing any traffic from leaking on your real IP during a reconnection. Split tunneling intentionally keeps two connections alive at the same time: one through the VPN, one direct. A kill switch is about protecting against accidental exposure; split tunneling is about deliberate, controlled routing.
Can my ISP see split-tunneled traffic?
Yes. Any traffic you route outside the VPN tunnel is visible to your ISP in the same way it would be without a VPN. Your ISP can see which sites and services those apps are connecting to. They cannot see the encrypted contents of HTTPS traffic — your bank’s website, for example, is still end-to-end encrypted by the browser — but the connection itself and the domain names are visible.
Does split tunneling work on iPhone?
For most VPN apps, no. Apple’s iOS security architecture prevents third-party apps from selectively routing traffic, and the majority of major providers do not offer split tunneling on iPhone. There are exceptions: Surfshark supports website-level exclusions on iOS, and IPVanish offers app-level split tunneling — one of the few consumer VPN apps to do so on iPhone. If full split tunneling across all apps is important to your setup, Android is the more capable platform. But check your specific provider’s iOS page first — the landscape has been slowly improving.
The Bottom Line
Split tunneling is not a shortcut or a compromise — it is a deliberate routing decision. Used correctly, it solves real problems that full tunnel mode cannot: printers that disappear, banking apps that block you, video calls that lag, local services that need your real location.
The key word is correctly. The risk is not the feature itself — it is using it without being intentional about which apps you expose. Route sensitive apps outside the tunnel by accident, or forget what you configured six months ago, and you have created a privacy gap you did not mean to.
The rule of thumb is simple: anything that genuinely needs your real IP address or local network access belongs outside the tunnel. Everything else stays inside it. Set it up deliberately, verify it with ipleak.net, and revisit the configuration if your app setup changes.
Done right, split tunneling gives you the privacy protection where it matters and the speed and compatibility where it does not — without having to choose between them.