Every VPN provider in the market makes the same claim: we do not keep logs. It appears on landing pages, in privacy policies, and in review summaries across the web. The phrase has become so ubiquitous that it has largely stopped meaning anything specific — and that is precisely the problem.
Understanding what a no-log policy actually covers requires drawing a line that most marketing copy deliberately blurs. There is a difference between privacy — hiding your activity from third parties like your ISP, your employer, or government surveillance — and anonymity — being untraceable even to the VPN provider itself. A VPN can deliver the first without delivering the second. A provider that never shares your data with anyone can still retain enough information about you to identify you if compelled by a court order. Whether it does is what a no-log policy is supposed to answer — and whether that answer is truthful is what this article helps you verify.
This guide covers what a no-log policy actually covers, what VPN providers are still permitted to collect without technically lying, and the framework used to verify a claim before trusting a provider with your privacy. If you are new to VPNs and want to understand how the technology works before evaluating privacy policies, start with how VPNs work and return here when you are ready to go deeper.
What “No-Log” Actually Means
A no-log VPN is a provider that commits not to collect or store records of your online activity — your browsing history, the IP addresses you connect to, your DNS queries, or the files you download. That definition covers what most people mean when they say they want a private VPN. The complication is that it does not cover everything a VPN server could theoretically record, and providers have historically exploited that gap.
The Three Types of Data a VPN Could Record
VPN data falls into three categories, each carrying a different level of privacy risk.
| Data type | What it includes | Privacy risk |
|---|---|---|
| Activity logs | URLs visited, DNS queries, files downloaded, application usage | Highest. This is the digital record of everything you did online. Reputable providers categorically do not collect this. |
| Connection metadata | Login timestamps, your original IP address, session duration, server used, bandwidth consumed | Medium. These are “quasi-identifiers” — individually innocuous, but combinable through correlation attacks to identify specific users. |
| Aggregated logs | Server load statistics, network performance metrics, regional traffic volumes | Low. Collected at a population level and cannot be linked to individual users when handled correctly. |
When a VPN provider advertises “no logs,” they almost always mean no activity logs. Connection metadata is the grey zone. Many providers collect some connection metadata for legitimate operational reasons — abuse prevention, simultaneous connection limits, subscription enforcement — but marketing copy rarely specifies this. The right question to ask is not “does this provider log?” but “which specific data fields does this provider record, and for how long?”
The Minimal Data Paradox
A true “zero-log” VPN is a misnomer. Every provider must retain some data to function as a business. Your email address is needed to manage your account. Your payment method is processed to handle billing. Subscription dates are recorded to enforce plan terms. None of this constitutes traffic logging, but it is data that can identify you if a court compels its disclosure.
The meaningful standard is not zero data of any kind — it is zero activity logs, minimal and time-limited connection metadata, and a transparent account data policy that tells you precisely what is held and for how long. A provider that is honest about this distinction is more trustworthy, not less, than one that claims nothing exists at all.
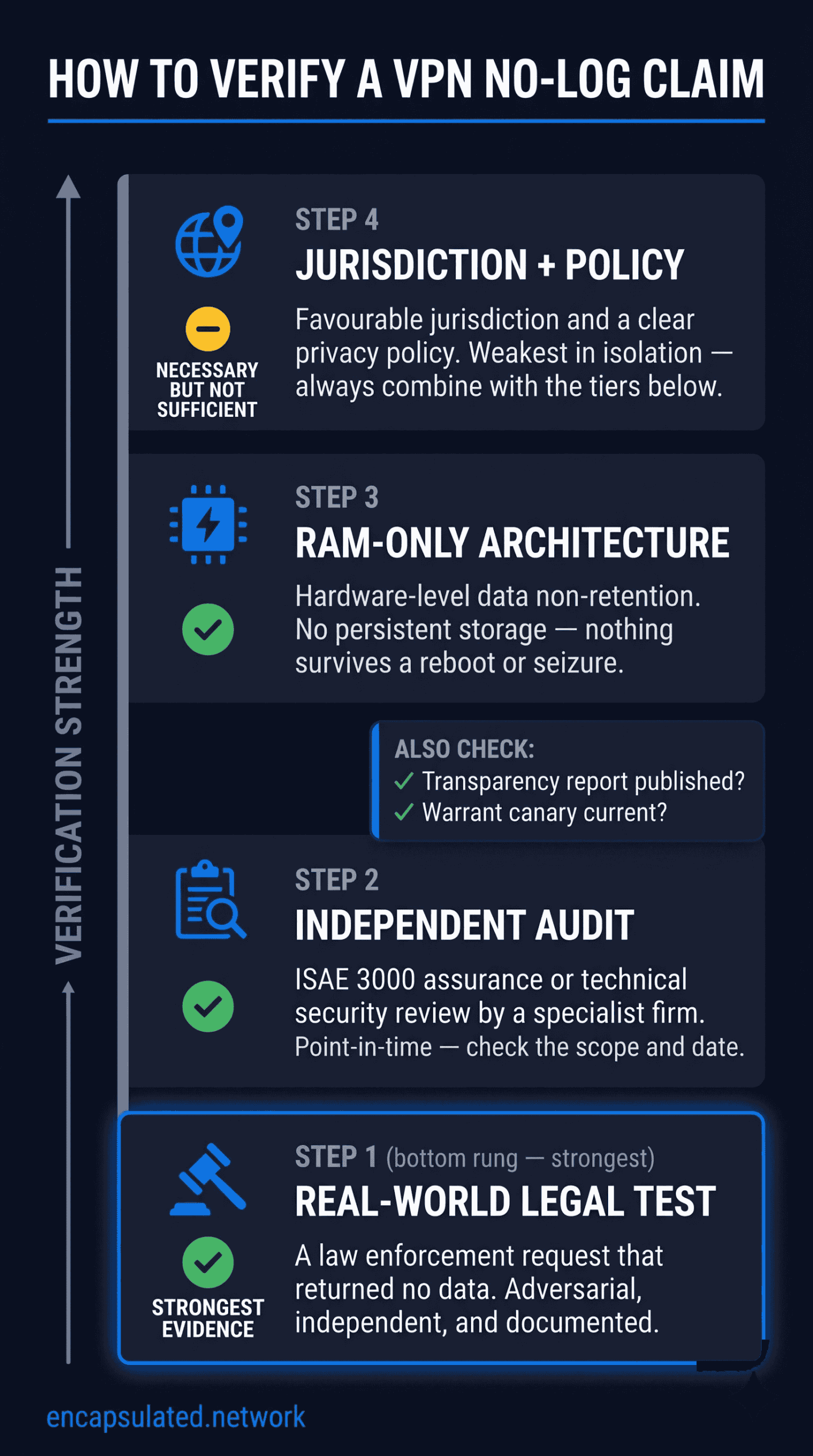
The Verification Framework: How to Separate Marketing from Reality
A privacy policy is the weakest form of evidence available. It is a self-attestation — the provider describing their own behaviour, with no external check. The verification methods below are ranked from the most externally validated to the most architecturally fundamental. A provider that can point to multiple layers of this framework is meaningfully more trustworthy than one that can point to only one.
a policy and a proof — weighted by how much independent evidence each
represents.
Independent Audits
An independent audit is a structured review of a provider’s infrastructure and data-handling practices by a firm with no commercial relationship to the outcome. In the context of VPN no-log claims, two categories of audit exist, and they are not the same thing.
Formal assurance engagements are conducted by firms such as KPMG and Deloitte under the ISAE 3000 standard — the International Standard on Assurance Engagements issued by the International Auditing and Assurance Standards Board. An ISAE 3000 engagement verifies that a provider’s internal controls and server configurations actually match the claims made in their published privacy policy. This is the most rigorous form of no-log verification available. SOC 2, the US-based equivalent from the AICPA, covers similar ground but has been used less frequently in published VPN no-log audits, likely because most privacy-focused providers are incorporated outside the United States. Both standards support Type 1 assessments (a point-in-time snapshot) and the more valuable Type 2 assessments (covering a defined period of ongoing operation).
Technical security audits are conducted by specialist firms such as Cure53, Securitum, Leviathan Security Group, and Schellman. These follow the audit firm’s own methodology rather than a formal assurance standard, and typically involve penetration testing, code review, and on-site server verification. They are complementary to formal assurance engagements — they probe for vulnerabilities rather than verifying policy compliance — and are often more technically detailed. Cure53, for example, has conducted annual full security audits of TunnelBear since 2017. Securitum conducts annual on-site no-log verification for Proton VPN.
Two caveats apply to any audit regardless of type. First, scope matters: an audit that reviewed a single app or browser extension does not verify server-side behaviour. Before drawing conclusions from an audit report, confirm that the review covered the provider’s full server infrastructure. Second, audits are point-in-time: a passed audit confirms behaviour up to the audit date, not beyond it. Annual or biannual audits are meaningful. A single report from several years ago is not.
Transparency Reports
A transparency report is a periodic disclosure by the provider detailing the legal requests they received during a given period — how many were received, how many were complied with, and in how many cases no responsive data existed. The final category is the verification moment: a provider that routinely reports “zero data available to produce” in response to legal requests is demonstrating its no-log policy in operation, not just in policy.
Transparency reports vary significantly in frequency and detail. Quarterly reports are more useful than annual ones. Reports that specify the nature of requests (subpoena, court order, law enforcement request) and the jurisdiction are more useful than those that report only totals. A provider that publishes no transparency report at all — particularly one operating in a jurisdiction with strong legal compulsion tools — is providing less assurance than its privacy policy implies.
Warrant Canaries
A warrant canary is a standing public statement that a provider has received no secret government orders — no gag orders, no national security letters, no sealed court orders — as of a specified date. The mechanism works in reverse: the canary is updated regularly as long as the statement remains true. If it disappears, or if the update stops, that signals something has changed.
Warrant canaries are a useful signal but not a guarantee. Their legal enforceability varies by jurisdiction. In the United States, courts have not definitively ruled on whether removing a canary constitutes protected speech or an impermissible act of defiance of a gag order. Treat a current, regularly updated canary as a positive indicator — and treat its absence or sudden disappearance as a reason to look more closely. Do not treat it as equivalent to a passed audit or a verified legal test.
RAM-Only Servers
RAM-only (diskless) servers represent a shift from policy to architecture. Rather than committing not to store data, a RAM-only server is physically incapable of retaining data across a reboot. The entire operating system and all session data run in volatile RAM. When power is cut — whether by a scheduled wipe, a routine maintenance reboot, or a physical server seizure — all data in memory is lost. Post-seizure forensic recovery is effectively impossible under normal operating conditions.
This is why RAM-only architecture is often described as a “forensic wall.” Software-based log deletion can be circumvented, audited retrospectively, or subjected to a legal hold order requiring preservation. Hardware-level non-retention removes the data before any legal process can reach it. There is nothing to compel production of because nothing persists.
However, this protection depends entirely on correct configuration. Three material caveats apply:
- Swap must be disabled. If the host operating system has swap enabled, the kernel can write RAM contents — potentially including sensitive session data — to persistent storage during memory pressure events. A properly configured RAM-only server must have swap completely disabled at the OS level.
- Kernel-level logging must be suppressed. Standard OS configurations include kernel functions that log metadata by default. A properly hardened RAM-only implementation must redirect or disable these processes.
- Live seizure offers no additional protection. A RAM-only server that is seized while still running can have its active memory accessed by an attacker with the right tools. RAM-only architecture protects against post-power-loss forensics, not against a live compromise of a running server.
RAM-only infrastructure requires a full server rebuild — it is not a software switch. Implementing it at scale represents a genuine operational commitment, which is why it carries meaningful weight as a verification signal.
| Verification method | What it proves | Key limitation |
|---|---|---|
| Formal assurance audit (ISAE 3000) | Policy matched infrastructure at audit date | Point-in-time; not a continuous guarantee |
| Technical security audit | Infrastructure withstood external technical scrutiny | Methodology varies by firm; scope may be limited |
| Transparency report | How the provider responded to real legal requests | Only covers disclosed requests; detail varies |
| Warrant canary | No secret orders received as of the canary date | Legal status complex; disappearance is the only signal |
| RAM-only servers | Hardware-level data non-retention; forensic wall | Requires correct configuration; no protection during live seizure |
When the Claim Has Been Tested: Real-World Legal Cases
The most reliable verification of a no-log policy is not an audit. It is a law enforcement request that returns nothing. When a government agency subpoenas a provider, seizes a server, or obtains a court order compelling disclosure — and the result is confirmation that no user data exists — that is a real-world test under adversarial conditions. No audit can replicate it.
Claims That Held Up
Private Internet Access (PIA) has been validated in two separate legal proceedings. In 2016, the FBI subpoenaed PIA in connection with a bomb threat investigation targeting schools and an airport. PIA was able to confirm only that the IP cluster used originated from the east coast of the United States and provide information about available payment methods. No user activity data existed to produce. In 2017, PIA was subpoenaed again during a federal hacking investigation in San Jose, California. PIA’s general counsel testified during the subsequent trial proceedings that no subscriber records matching the suspect’s identifiers existed in PIA’s systems. The defendant was prosecuted on other evidence. Both cases are a matter of public court record.
Mullvad VPN was subject to a physical law enforcement operation in April 2023, when Swedish National Operations Department officers arrived at Mullvad’s Gothenburg office executing a search warrant. The warrant originated from a European Investigation Order issued by German authorities in connection with a 2021 cyberattack targeting municipal institutions in Mecklenburg-Western Pomerania. Officers intended to seize computers containing customer data. Mullvad demonstrated that no such data existed on any of its systems. After consulting the prosecutor on-site, police left without taking anything and without any customer information. Mullvad confirmed this was the first search warrant the company had received in its fourteen-year history — and that even if servers had been taken, no customer data would have been on them.
ExpressVPN had a server physically seized by Turkish authorities in January 2017, in connection with an investigation into who deleted the Gmail and Facebook accounts and conversations of the assassin of the Russian ambassador in Ankara — off-duty police officer Mevlüt Mert Altıntaş — in what Turkish investigators characterised as an attempt to destroy evidence. The seizure yielded no useful user information. ExpressVPN confirmed to Turkish investigators that it holds no connection logs or activity logs. ExpressVPN subsequently stopped using physical servers in Turkey.
Claims That Collapsed
Not every no-log claim has survived contact with legal pressure.
PureVPN cooperated with an FBI investigation in 2017 that resulted in the arrest of a Massachusetts man for cyberstalking. The FBI complaint details that PureVPN provided connection logs showing that the provider’s service had been accessed by the same customer from two originating IP addresses — the suspect’s home internet connection and his employer’s network. This was sufficient to link VPN usage to the individual. PureVPN’s marketing at the time stated “we do not keep logs of your activities.” The fine print of its privacy policy, however, did reference collection of IP addresses and connection timestamps. PureVPN had been collecting connection metadata all along — and advertising a no-log policy that its own privacy policy did not fully support. This case is a precise real-world demonstration of the grey zone defined in Section II: the provider never claimed not to keep connection metadata, but marketed broadly as a no-log service. PureVPN subsequently commissioned a KPMG audit in 2020 to verify its revised policy.
IPVanish provided subscriber information and connection and disconnection timestamps to the US Department of Homeland Security in 2016 during an investigation involving child exploitation material. IPVanish’s homepage at the time advertised a “strict zero-logs policy.” The data provided was sufficient to identify the suspect. IPVanish changed ownership in 2017 and has since completed independent no-log audits with Leviathan Security Group (2022) and Schellman (2025). The current operator’s policy and the independently verified policy post-2017 are a separate matter from the 2016 failure — but the original case remains a documented instance of a no-log claim that did not hold under legal pressure.
Both cases illustrate the same lesson: the meaningful question is not what a provider’s privacy page says, but what data fields are specifically listed as not collected, and whether an independent third party has verified the technical implementation of that claim.
Jurisdiction and the Legal Ceiling of Privacy
A provider’s jurisdiction determines the legal environment it operates within — the data retention laws it must comply with, the intelligence agencies that can compel disclosure, and the international cooperation frameworks it is subject to. Jurisdiction sets a ceiling on what privacy a provider can offer, regardless of its intentions.
The Surveillance Alliance Map
The intelligence-sharing alliances relevant to VPN jurisdiction are structured in three tiers.
Five Eyes is the foundational alliance: the United States, United Kingdom, Canada, Australia, and New Zealand. It is based on the UKUSA Agreement, a formal signals intelligence treaty signed in March 1946 and expanded to include Canada in 1948 and Australia and New Zealand in 1956, declassified in 2010. Intelligence collected by any Five Eyes member is shared across all five.
Nine Eyes extends the Five Eyes with Denmark, France, the Netherlands, and Norway. This is an informal intelligence-sharing arrangement rather than a formal treaty.
Fourteen Eyes — officially known as SIGINT Seniors Europe (SSEUR) — adds Germany, Belgium, Italy, Sweden, and Spain to the Nine Eyes. Again informal, operating since approximately 1982, and largely unknown to the public until the Snowden disclosures in 2013. Additional countries cooperate with SSEUR on a bilateral or associated basis, though the specific membership of these arrangements is not fully documented in declassified materials and should not be treated as a fixed or confirmed list.
The practical implication: a VPN provider incorporated in a Fourteen Eyes country operates within a legal environment where intelligence agencies from up to fourteen governments may have compulsion tools available, and where data shared with one agency may flow to others. This is the ceiling. A provider with a genuine no-log policy — one with no data to produce — is less affected by this ceiling than one that retains connection metadata.
Privacy Havens and Legal Ambiguities
British Virgin Islands is a favourable jurisdiction. The BVI Data Protection Act 2021 is an EU-style data protection law that actively requires data not be kept longer than necessary — reinforcing rather than conflicting with a no-log policy. There are no telecommunications-specific data retention mandates. Any foreign government request for data must pass through the BVI High Court, requiring dual criminality and a high evidentiary standard. The BVI is not a member of any intelligence-sharing alliance.
Switzerland does not currently impose mandatory data retention obligations on VPN providers. The revised Federal Act on Data Protection (nFADP), effective since September 2023, emphasises data minimisation and purpose limitation without imposing retention requirements. Switzerland’s Telecommunications Act imposes retention obligations on licensed telecommunications carriers, but VPN providers have not been classified as such under this framework. However, a proposed amendment to Switzerland’s surveillance ordinance (VÜPF) — currently paused pending an independent impact study — would expand metadata retention requirements to VPN providers. Several Swiss-based providers have publicly expressed concern about this development. Switzerland’s status as a favourable jurisdiction is current but under active legislative review.
Panama is widely cited as a favourable jurisdiction, and several major providers are incorporated there. The situation requires qualification. Panama’s Law 51 of 2009 requires telecommunication service providers to retain connection metadata for six months. Whether VPN providers fall within the statute’s definition of a telecommunication service provider is a matter of ongoing legal interpretation — a Panamanian law firm has published analysis arguing they may be covered, and the district attorney’s office has reportedly been processing international information requests directed at Panama-incorporated VPN providers. No published case has yet compelled a Panama-based VPN provider to surrender logs, and major providers incorporated there have passed multiple independent audits. Panama cannot be characterised as unambiguously retention-free, however — the legal ambiguity is real.
Iceland lacks mandatory data retention laws applicable to VPN providers. As a member of the European Economic Area but not the EU, Iceland was not subject to the EU Data Retention Directive. Iceland participates in NATO and has some international cooperation arrangements, but has no data retention framework that would oblige a VPN provider to store user metadata.
Architecture Over Geography
Jurisdiction matters — but it is not the only variable. The strongest counter-argument to jurisdiction-focused analysis is architectural: if a VPN provider genuinely cannot store data — RAM-only servers, strict no-log implementation, no account data beyond payment processing — then its physical location becomes less relevant. There is no data to compel production of. A court order directed at a provider with nothing to produce returns nothing, regardless of the jurisdiction that issued it.
Jurisdiction sets the legal ceiling. Architecture determines whether there is anything under that ceiling within reach. A provider in a favourable jurisdiction with poor technical implementation is less trustworthy than a provider in a less favourable jurisdiction with verified RAM-only infrastructure and multiple passed audits. Assess both dimensions — and weight the technical implementation more heavily when the audit record is strong. For a deeper look at how your data moves across the tunnel at the protocol level, see our guide to how your data moves across the tunnel.
How to Read a Privacy Policy Without a Headache
Most VPN privacy policies are written by lawyers for compliance purposes, not by engineers for clarity. Reading them well requires knowing what to look for and what to treat as a warning sign.
Green flags — indicators of a credible no-log policy:
- Specific data fields listed as explicitly not collected — not vague assurances like “we don’t log browsing activity,” but enumerated field-level commitments (“we do not store originating IP addresses, DNS queries, connection timestamps, or bandwidth usage per user”)
- A linked audit report dated within the last eighteen months, with the scope of the review clearly stated
- Explicit retention periods for account data — how long your email address, payment records, and subscription dates are held
- A jurisdiction with no mandatory data retention laws applicable to VPN providers
- Acceptance of anonymous payment methods (Monero is the strongest example; providers including Mullvad and IVPN accept it directly with no email required)
- A documented real-world legal test where no data was produced in response to a law enforcement request
- A regularly updated transparency report
Red Flags in a Privacy Policy
- Vague qualifiers. Phrases like “minimal logging for service quality,” “technical data only,” or “aggregate information to improve performance” define no scope and create no enforceable commitment. They are placeholders, not policies.
- No audit, or an outdated one. An audit older than three years, or an audit that covered only a mobile app rather than the server infrastructure, provides limited assurance about current server-side behaviour.
- “We do not sell your data.” This says nothing about what is collected. A provider can collect extensive metadata and never sell it to anyone — while still retaining it in a form that is accessible to law enforcement.
- No transparency report and no warrant canary. Either is acceptable; neither is a gap in accountability that a thoughtful privacy policy would leave unfilled.
- A free VPN with no clear revenue model. VPN infrastructure is expensive to operate. If the service is free and there is no subscription revenue, the business model requires scrutiny. Data monetisation is the most common answer to this question in the free VPN market. A privacy policy from a free provider that offers no clear explanation of how the service is funded warrants maximum scepticism.
- Infrequent policy updates with no changelog. A provider that actively manages its no-log commitments will update its privacy policy as its practices evolve and note what changed. A policy that has not been touched in years — particularly one that predates any audit — is likely not being actively maintained.
Frequently Asked Questions
What does no-log mean on a VPN?
A no-log VPN is one that does not collect or store records of your online activity — specifically your browsing history, DNS queries, the IP addresses of sites you visit, and the files you download. In practice, most providers distinguish between activity logs (which they do not keep) and connection metadata such as login timestamps or bandwidth consumed (which some do retain in limited form). A credible no-log policy specifies which data fields are not collected, rather than making a broad claim without enumeration.
Can a VPN be truly no-log?
A VPN can be genuinely no-log with respect to your browsing activity and connection behaviour. What it cannot eliminate entirely is account data — your email address, payment method, and subscription dates — which must exist for the service to function. The meaningful standard is zero activity logs, minimal and time-limited connection metadata, and a transparent account data policy. Providers who are honest about what account data they hold and for how long are generally more trustworthy than those claiming nothing exists at all.
How do I know if my VPN keeps logs?
Read the privacy policy carefully, looking for specific field-level commitments rather than broad assurances. Then verify: look for a current independent audit with full server infrastructure scope, check whether the provider publishes transparency reports, and search for any documented legal cases where the provider was asked to produce data. A provider that has passed a formal ISAE 3000 assurance engagement and has a real-world legal test on record is giving you two independent sources of confirmation.
What is a RAM-only VPN server?
A RAM-only server runs its entire operating system and session data in volatile memory (RAM) rather than on physical hard drives. When the server loses power — whether through a reboot, scheduled wipe, or physical seizure — all data in RAM is lost and cannot be forensically recovered. This is described as a “forensic wall”: there is nothing persistent on the server for an investigator to recover after the fact. The protection depends on correct configuration — swap must be disabled and kernel logging suppressed — and does not apply if the server is seized while still running.
Does a no-log VPN protect me from law enforcement?
A genuine no-log VPN protects you from law enforcement disclosure only insofar as there is no data to disclose. If a provider holds no activity logs, no connection metadata, and no account data beyond what is needed for billing — and that is independently verified — then a law enforcement request returns nothing. The cases of Private Internet Access and Mullvad VPN demonstrate this outcome under real conditions. The cases of PureVPN and IPVanish demonstrate what happens when the technical implementation does not match the marketing claim. The policy is only as protective as the data architecture behind it.
What is a VPN audit?
A VPN audit is a review of a provider’s infrastructure and data-handling practices by an independent third party. Formal assurance audits — conducted by firms like KPMG and Deloitte under the ISAE 3000 standard — verify that internal server configurations and controls match what the provider’s privacy policy claims. Technical security audits — conducted by specialists like Cure53 and Securitum — use penetration testing and on-site inspection to verify that no data is being retained and that the infrastructure is not vulnerable to compromise. Both types are point-in-time: they confirm behaviour up to the audit date, not beyond it. Annual or biannual audits are meaningful; a single report from several years ago is not.
Is a VPN in a 14 Eyes country safe?
Jurisdiction affects the legal ceiling of what a provider can offer — the compulsion tools available to government agencies and the intelligence-sharing obligations that apply. A provider in a Fourteen Eyes country operates within a more legally exposed environment than one in a jurisdiction with no data retention laws and no alliance membership. However, jurisdiction is not the only variable. A provider in a less favourable jurisdiction with RAM-only infrastructure, a passed ISAE 3000 audit, and a documented legal test where no data was produced may be more trustworthy in practice than a provider in a privacy haven with no independent verification of any kind. Assess the technical implementation alongside the geography.
The Trustless Future of Digital Privacy
The VPN industry has spent years competing on the strength of privacy claims rather than the strength of privacy architecture. That is changing. The most rigorous providers are moving toward what might be called system transparency: infrastructure designed so that users do not need to trust the provider’s word at all, because the architecture makes log retention physically impossible and independent auditors confirm that architecture publicly.
The checklist below summarises what that looks like in practice — four indicators of a trustworthy no-log claim, weighted by how much independent evidence each represents:
- Passed a real-world legal test with no data produced. A law enforcement request that returned nothing is the strongest validation available. It is adversarial, independent, and documented.
- Current independent audit with full infrastructure scope. An ISAE 3000 or SOC 2 assurance engagement, or a comprehensive technical audit by a specialist firm, completed within the last eighteen months and covering the provider’s complete server infrastructure.
- RAM-only server architecture. Hardware-level data non-retention that makes post-seizure forensics effectively impossible when correctly implemented.
- Favourable jurisdiction with no mandatory data retention. A legal environment that does not undermine the provider’s technical commitments through compulsion.
No provider that claims a no-log policy but cannot point to any of these indicators is asking you to take their word for it. That is a reasonable thing to ask for — and an increasingly unnecessary one to accept.
